I guess I could operate without a computer but it would be a challenge. Almost as challenging as working
with one.
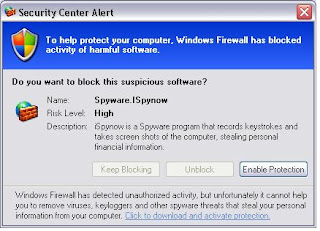
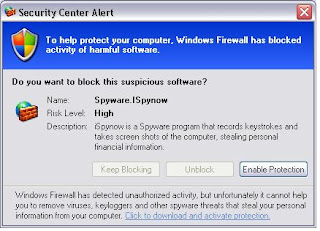
Dec. 2 I got a Fake message from out in cyberspace, that I was infected with a virus (which I wasn't) and the only options seemed to be to click "Enable Protection", This click sent me to a "rogue" website called "Personal Defender 2009", wanting to sell "protection" from the "virus". I did not buy, and I closed the site. But my click on the "Enable Protection" (see image above) was enough to load some malware to my computer.
Spyware.iSpyNow is fake windows alert which is secretly installed by severe trojans. In point of fact, Spyware.iSpyNow is not a keylogger but it is a part of severe trojan that’s main motive to sale the
rogue antispyware software such as Personal Defender 2009 and so on.
While it was not too difficult in the end to get rid of this malware/trojan, it was a tedious proccess in finding out how? I do not wish it on anyone of course but here are the steps taken to remove any that are infected. (contact me if you need help)
These are Marcin Kleczynski's instructions (
Malwarebytes' Anti-Malware) Free
1. Download Malwarebytes from a clean, non-infected computer. Also download a more recent update of virus definitions from the malewarebytes website (the spyware prevents the program from updating) - http://www.gt500.org/malwarebytes/database.jsp
2. In specific regard to the Malewarebytes program “the standard file name will be mbam-setup.exe, please rename it to just setup.exe. Once the installation completes, please navigate to C:\Program Files\Malwarebytes’ Anti-Malware and rename mbam.exe to file.exe.”
3. Restart your machine
4. Double click and install the virus definitions for Malewarebytes (the one’s you downloaded before from the web).
5. Run Malewarebytes by clicking file.exe in the Malewarebytes program files folder.
6. If you haven’t already done so, use the “File Assassin” tool to corrupt the .exe and .dll files stored in your Google folder.
7. Run the scan under the “Scanner” tab by clicking Perform Full Scan.
8. The software should take you through the rest. Delete bad files and restart.
9. Your anti-virus programs should now work, BUT you are not done. Open up Malewarebytes again and update the virus definitions (the web version is slightly older).
10. Run the scan again.
*************************************
Click
here for a long discussion on this (or not). The above was from post #71 in the discussion.
In the same discussion "Frewheelin Frank" posted
“Where did this thing come from?”
Several people have asked a similar question, so I thought I’d answer.
Sometimes from a hacked web page which diverts your browser to a fake virus scan or security warning looking very much like a real virus scanner or Microsoft security warning. This sort of attack depends on fooling the user into thinking that the scan or warning is legitimate and accepting the download of malicious software and installing it- into clicking ‘yes’ to a dialogue. (This is often called ’social engineering’, although a more apt term would be trickery.)
Sometimes these scam programs are installed by ‘drive by’ download: you visit a hacked web site, and the page contains (or diverts to) an ‘exploit’, which is a way of attacking your computer via a known security vulnerability in software on the computer.
Again I hope you do not need the information, but it is proving to be "out there the past few weeks. It seems that I got the original false Security warning (image) after using Google reader.